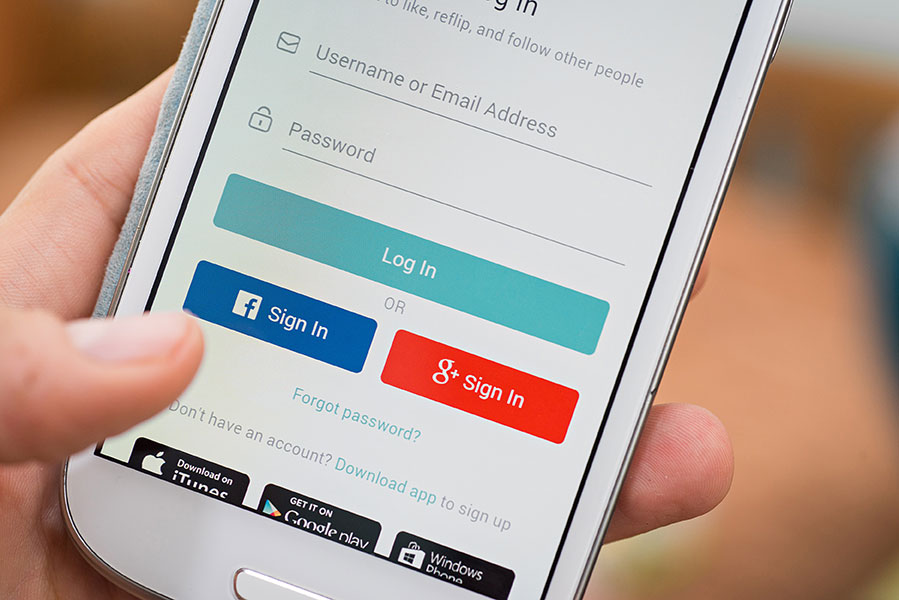
In today’s digital age, the convenience of logging in with your Facebook or Google account seems like a time-saving solution. Many online platforms offer this option to streamline the account creation process, but is it really the best choice for users concerned about their privacy and security? “Log In with Facebook or Google” poses significant risks of which users should be aware. In this blog post, we explore the drawbacks of this seemingly convenient authentication method.
Privacy Concerns
When you log in with Facebook or Google, you grant the platform access to a considerable amount of personal information. While some services only request basic details, others may seek permission to access your friend list, email contacts, and even post on your behalf. This not only compromises your privacy but also raises questions about how your data might be used by the platform.
Single Point of Failure
By linking your account to a social media or Google account, you create a single point of failure. If your Facebook or Google account is compromised, all linked accounts become vulnerable. This interconnectedness increases the potential impact of a security breach, making it easier for hackers to gain unauthorized access to multiple services.
Limited Control Over Information
When you log in with a social media or Google account, you relinquish control over the information you share with the third-party service. This lack of control can lead to unexpected data sharing, targeted advertising, and other privacy-related issues. Citynet believes that users should have more say in how their data is used and shared.
Data Harvesting and Tracking
Logging in with Facebook or Google often involves consent to the platform’s terms of service, which may include clauses allowing the collection and analysis of user data for advertising purposes. This data harvesting can lead to targeted ads and the creation of detailed user profiles, contributing to a more intrusive online experience.
Limited Account Recovery Options
If your Facebook or Google account is ever compromised, recovering access to your linked accounts can become a cumbersome process. Citynet recommends diversifying your authentication methods to enhance security and facilitate easier account recovery in case of an incident.
While the allure of a quick and easy login process is understandable, consider these potential drawbacks. The risks associated with “Log In with Facebook or Google” extend beyond mere convenience and can compromise user privacy, security, and control over personal information. Choose more secure and privacy-focused authentication methods for creating online accounts to increase your security.