About: Blog

Why Every Home Needs a Guest WiFi Network
Most people think of WiFi as a single network. A friend visits, asks for the password, and you share it without much thought. What many

Know Your Numbers: A Simple Guide to Internet Speed Tests
Nothing is more frustrating than being in the middle of a video call and experiencing choppy, pixelated picture or audio. Or, if you’re trying to

Reduce the Energy Costs of Your Tech
Most of us think about saving energy by turning off lights or adjusting the thermostat. But today’s homes run on something just as important: connectivity.

Host a Virtual Game Night Without Lag
Hosting a virtual game night is a great way to stay connected with your friends and family, especially when everyone is joining in from different

Before You Dig in West Virginia: Why Calling 811 Matters
Spring has arrived in West Virginia, and with it comes a surge of outdoor projects—planting trees, installing fences, landscaping, and home improvements. Before you start
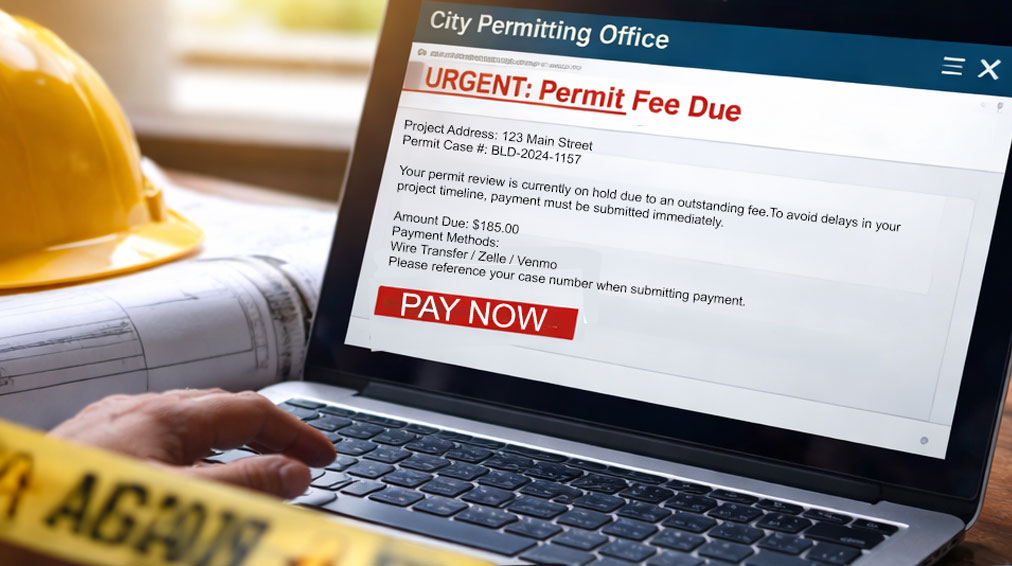
Scammers Are Targeting Home Projects—Here’s What to Watch
If you’re building, renovating, or improving your home, there’s a new scam you need to watch for—and it’s catching people at exactly the wrong time.

Stop the Buffer: How to Get the Most from Your Streaming Experience
There’s nothing more frustrating than getting to the final seconds of a close game—only to see the spinning buffering wheel right before the winning shot.

Phone Photography Tips: Take Better Photos This Spring
Capture Spring Like a Pro — With Just Your Phone Spring is one of the most photogenic times of year—blooming flowers, longer golden-hour light, and

How Long Attackers Stay in a Network Before They’re Discovered
When people imagine a cyberattack, they often picture a dramatic event — systems suddenly shutting down or files becoming encrypted. But many cyber incidents don’t
Protecting Devices Before the Next Storm
Stay Connected When the Power Goes Out High winds, heavy rain, lightning, ice, and even wildfires can knock out power in an instant. And when

How Most Cyberattacks Actually Start
It’s usually not a sophisticated hack — it’s a moment of trust. Many organizations imagine cyberattacks as highly technical breaches targeting servers or networks. In
5 Critical Mistakes to Avoid During a Cyberattack
Think your business may already be compromised? See the warning signs and response steps here Even well-intentioned actions can make a cyber incident worse Cyberattacks

The Smart Pet Home: Technology That’s Changing How We Care for Our Pets
Being a pet owner today looks a lot different than it did even a few years ago. From checking in on your dog while you’re

Spring Clean Your Home Office (Inside and Out)
Spring is right around the corner. While you’re planning to declutter closets and organize the garage, don’t forget one of the most important spaces in

You’ve Been Served… a Scam!
Beware of Fake Toll Violation Text Messages Cybercriminals are constantly evolving their tactics to trick people into giving up sensitive information. One of the latest

Cybercriminals Are Now Calling Your Employees
Is Your Business Prepared? Cyber threats are evolving, and one of the fastest-growing tactics right now is social engineering through trusted communication platforms. Instead of trying

The New Employee Is Your Biggest Security Risk
(And It’s Not Their Fault) When businesses think about cybersecurity risk, they often picture hackers, ransomware, or sophisticated phishing attacks. But one of the most
Shadow IT: The Apps Your Employees Use That IT Doesn’t Know About
When most businesses think about cybersecurity risk, they picture hackers breaking in from the outside. But one of the fastest-growing risks isn’t external at all.

The New Reality of Cyber Insurance Requirements for Small Businesses
Cyber insurance used to feel like a safety net. Today, it’s starting to feel more like an application for a mortgage. Across the country, insurance
Citynet and Red Siege Webinar Inside the Attacker’s Playbook
Cybersecurity isn’t just about defense — it’s about understanding how real attackers think. Join Citynet’s Craig Behr and Red Siege’s Tim Medin for an upcoming

Cyber Protection During Tax Season: What You Need to Know
Tax season is stressful enough without worrying about cybercriminals. Unfortunately, this time of year is one of the busiest for online scams, phishing attacks, and

What Is a Romance or Dating Scam?
Looking for love? You may be able to find your person online. The stigma of online dating has long since passed. In fact, in 2023, Pew

Simple Tech That Makes Cold Weather Easier to Bear
Winter can be tough. With cold temperatures, snow and ice, dry air, and higher heating bills, it’s no wonder the animals head into hibernation! Unlike
Power Cycling Your Router
It is important to have a good grasp of how your router works, as it can impact your wireless connectivity. If you are experiencing problems

Be Prepared for Storms!
Storms are bound to knock out power and the internet from time to time. Lightning strikes and power surges can easily damage your technology. Overnight

Why Fiber Is the Foundation of Reliable Business Operations
In today’s always-connected business environment, reliability isn’t optional. Cloud applications, phone systems, cybersecurity tools, backups, and day-to-day operations all depend on one thing working consistently:

Understanding WiFi Signal Strength and Tips for Better Coverage
Even with fast fiber internet, many people still struggle with weak WiFi, dead zones, or slow speeds in certain rooms. Walls, distance, old devices, and

The Emergency Information Everyone Needs on Their Phone
Our cell phones give us the modern convenience of access to emergency services almost anywhere. But, in the case of an emergency, first responders may

AI & Cybersecurity in 2026: What Business Leaders Need to Prepare for Now
Citynet Managed Services Perspective As we move into 2026, artificial intelligence is no longer a future consideration in cybersecurity — it’s the defining force shaping

Small IT Team, Big Responsibility: How Managed Services Fill the Gaps
For many small and mid-sized organizations, IT responsibility rests on the shoulders of one or just a few people. These teams are expected to keep

Reactive IT vs Proactive IT: The Hidden Cost of Downtime for Small Businesses
For small and mid-sized businesses, reactive IT support often leads to unexpected downtime, lost productivity, and higher long-term costs—especially when compared to proactive managed IT

CitynetTV & Internet Tip Sheet
TV Remote Step 1: Press and hold the ‘setup’ button at the top right of your remote until the LED blinks twice. Step 2: Press
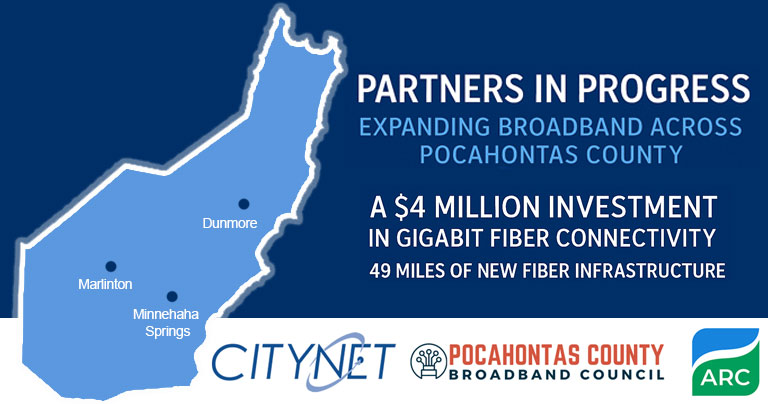
Citynet Joins Partners to Celebrate Broadband Expansion in Pocahontas County
Marlinton, WV – November 4, 2025 – Citynet is proud to join the Pocahontas County Broadband Council, the Pocahontas County Commission, and the Appalachian Regional Commission (ARC) in celebrating

Backing Up Your Digital Life
Uh oh…. Your computer’s hard drive failed. The latest update crashed your phone. Your tablet went missing at the airport. You accidentally hit the delete

Trusted Email. Fake File. Real Danger.
Beware of Business Email Compromise (BEC) Scams Disguised as File-Sharing Requests! Cybercriminals are getting more creative every day. And one of their favorite tricks right
Tyler County to Celebrate USDA ReConnect Broadband Project with Citynet
Sistersville, WV – October 1, 2025 – The Tyler County Development Authority, in partnership with the United States Department of Agriculture (USDA) and Citynet, will host

When “IT Support” Isn’t Who They Claim to Be
Cybercriminals are getting craftier, and one of the latest tricks is designed to make you think help is just a call away. Unfortunately, it’s not

Think Antivirus Is Enough? Think Again.
For years, businesses have relied on antivirus software, firewalls, and email filters to defend against cyberattacks. These tools are important, but on their own, they’re
VPNs Explained
You may have heard the term “VPN” tossed around when people talk about internet safety, remote work, or protecting personal information online. You may even

Estate Planning for Your Digital Assets
You’ve probably seen the joke online: “If I die, delete my browsing history.” It’s meant to be funny, but it’s rooted in a real and

Digital Security Tips for Modern Cars
Computers, phones, watches, tablets … mobile technology is both a convenience and a risk of your personal details in the hands of others. We keep

Host the Perfect Football Streaming Party
Streaming the big game with friends this weekend? From Wi-Fi tips to snack table must-haves, CITYNET has your game-day playbook for hosting the perfect football

Build a New Home with Connectivity in Mind
When you build a home, you make plans for plumbing, electrical, and insulation. Why not also plan for internet connectivity? With the average household now

Smart Home Tech for Your Pets
Smart home tech isn’t just for people. Your pets deserve great WiFi, too! From cameras to smart feeders to GPS collars, check out how CITYNET’s

Watch Out for This Amazon Text Scam
A new text message scam is making the rounds, and it’s designed to look like it came straight from Amazon. The message claims that an

Tech Talk Decoded: Top Terms & Acronyms You Should Know in 2025
Technology changes fast, and so does the language that comes with it. Whether you’re talking about internet speeds, cybersecurity tools, or the latest Wi-Fi standards, new
Why Immutable Backup Should Be Part of Your Strategy
SMBs, Don’t Let Ransomware Destroy Your Business! For small and medium-sized businesses, a single cyberattack can be devastating. Whether it’s ransomware, accidental deletion, or insider

The Scam You Haven’t Heard About Yet: Deepfake Voicemail Fraud
Cybercriminals are getting smarter – and sneakier. One of the fastest-growing threats targeting businesses right now? Deepfake voicemail scams. How It Works Attackers use AI

