90% involve social engineering (see infographic below)
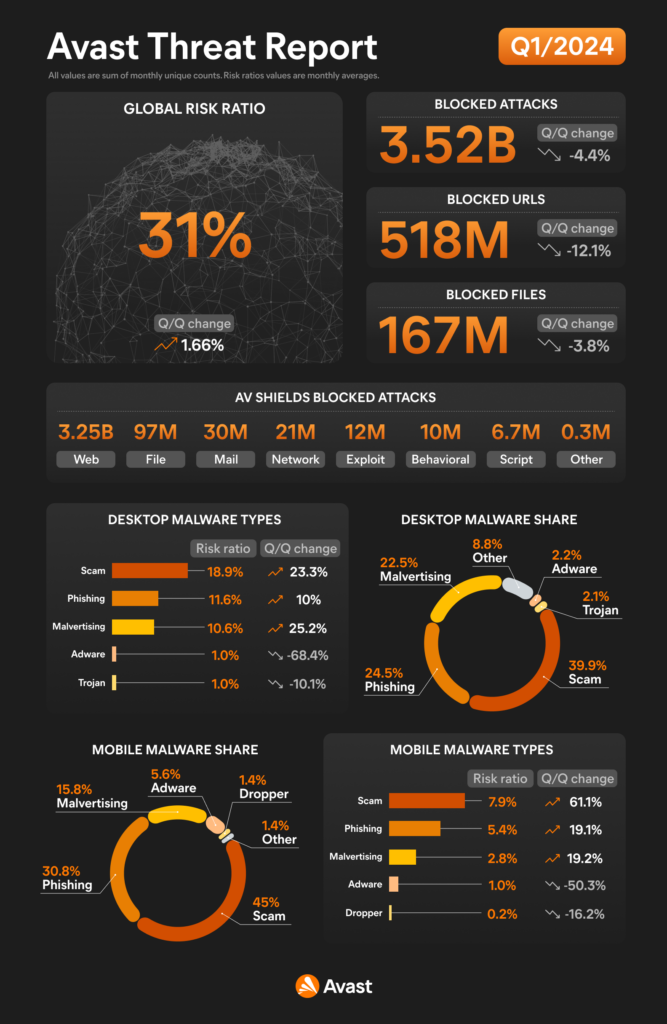
In the realm of cybersecurity, the ability to predict and prepare for attacks is invaluable. Much like how a small sample of votes can accurately predict a presidential election, analyzing a large dataset of cyber attacks can reveal critical trends and threats. Citynet partner, Avast, recently released Q1/2024 Threat Report, which analyzes over 3.5 billion cyber attacks, we gain a clear and accurate reflection of the current cyber threat landscape.
Key Insights from the Report
The Avast report highlights several crucial findings that organizations need to be aware of to bolster their defenses effectively. Here are the main takeaways:
- Scams and Phishing are Predominant Scams and phishing attacks are the most common forms of malware attacks. These types of attacks are not only prevalent but also highly effective due to their reliance on social engineering techniques.
- Social Engineering Attacks are Rampant
- Mobile Attacks: A staggering 90% of mobile attacks involved social engineering.
- Desktop Attacks: Similarly, 87% of desktop attacks leveraged social engineering tactics.
These statistics underscore the importance of understanding and defending against social engineering attacks, which are designed to trick users into divulging sensitive information or performing actions that compromise security.
What This Means for Your Organization
Based on the data, here are the primary characteristics of the attacks you are most likely to encounter:
- Web and Email Vectors: The majority of attacks originate from the web or via email. This means that these two areas are the primary channels through which your organization can be targeted.
- Social Engineering Elements: Attackers use social engineering to deceive users, making it a critical aspect of many cyber attacks. This includes scams, phishing attempts, and other tactics designed to manipulate individuals.
- Intent to Compromise: The goal of these attacks is typically to scam users, steal credentials, gain remote access, install malware, or commit digital fraud.
Strengthening Your Cyber Defenses
Given these insights, organizations should take a two-pronged approach to enhance their cybersecurity posture:
- Enhance Security Controls for Email and Web Implement robust security solutions that provide proactive protection against malicious content on both email and web platforms. This includes advanced email filtering, web filtering, and anti-phishing technologies.
- Invest in Security Awareness Training Educate and empower your employees to recognize and respond to social engineering attacks. Security awareness training can significantly reduce the risk of user engagement with malicious content and enhance your overall security culture. Citynet partners with the industry leader in the security awareness training area, KnowBe4. Learn more about KnowBe4’s comprehensive training and get a free demo for your organization.
Citynet Can Help
The Avast Q1/2024 Threat Report provides invaluable insights into the current state of cyber threats. By understanding the predominant attack vectors and tactics, organizations can better prepare and protect themselves. Focus on strengthening your defenses around email and web security, and invest in training your workforce to recognize and thwart social engineering attacks. This comprehensive approach will help mitigate risks and safeguard your organization against the ever-evolving cyber threat landscape.
Let Citynet work with you to create a strategic cybersecurity plan. Our approach combines industry-leading solutions along with expert deployment by Citynet’s team of cybersecurity experts, backed by simply outstanding customer support.
Stay safe, stay informed, and prioritize your cybersecurity efforts to keep your organization resilient against cyber attacks.