Most universities provide students with email addresses from the university’s official domain. For example, a student's email address could be firstname[at]harvard[dot]edu. Since these email addresses use real university domains, cybercriminals try to gain access to student email
Do you regularly use your debit card for online purchases? Do you have payment information saved on online shopping accounts? Do you use autofill to enter your payment information? If you answered yes to any of these
Did You Know? CityCare by Citynet offers worry-free network management, including software management on covered devices. Learn more! We close this year’s Cybersecurity Awareness program with a look at the danger presented by phishing. What is Phishing?
Google Translate is a free service that you can use to translate text from one language to another. Since Google Translate is a Google product, many people view it as a sign that a webpage is trustworthy.
One of the most common and successful tricks cyber criminals use to trigger you into falling for their scams is fake “stressor events”. In this context, “stressor events”, are shocking or compromising situations that inflict fear or
Did You Know? CityCare by Citynet offers worry-free network management, including software management on covered devices. Learn more! Week three of National Cybersecurity Month is here, and this week we focus on the important task of updating
Many people see email as a convenient and effective way to receive information. Popular banks have even started using email as a primary method of communication to send account updates to their customers. Now, cybercriminals are imitating
What is it? Multi-factor Authentication (MFA) is the process of verifying that you are who you claim to be when logging in to a device or an account. If you're reading this from your work computer, you
When a natural disaster strikes, many people rely on insurance providers for disaster relief to help them pay for damages to property. Unfortunately, cybercriminals can take advantage of this vulnerable situation by manipulating you into sharing sensitive
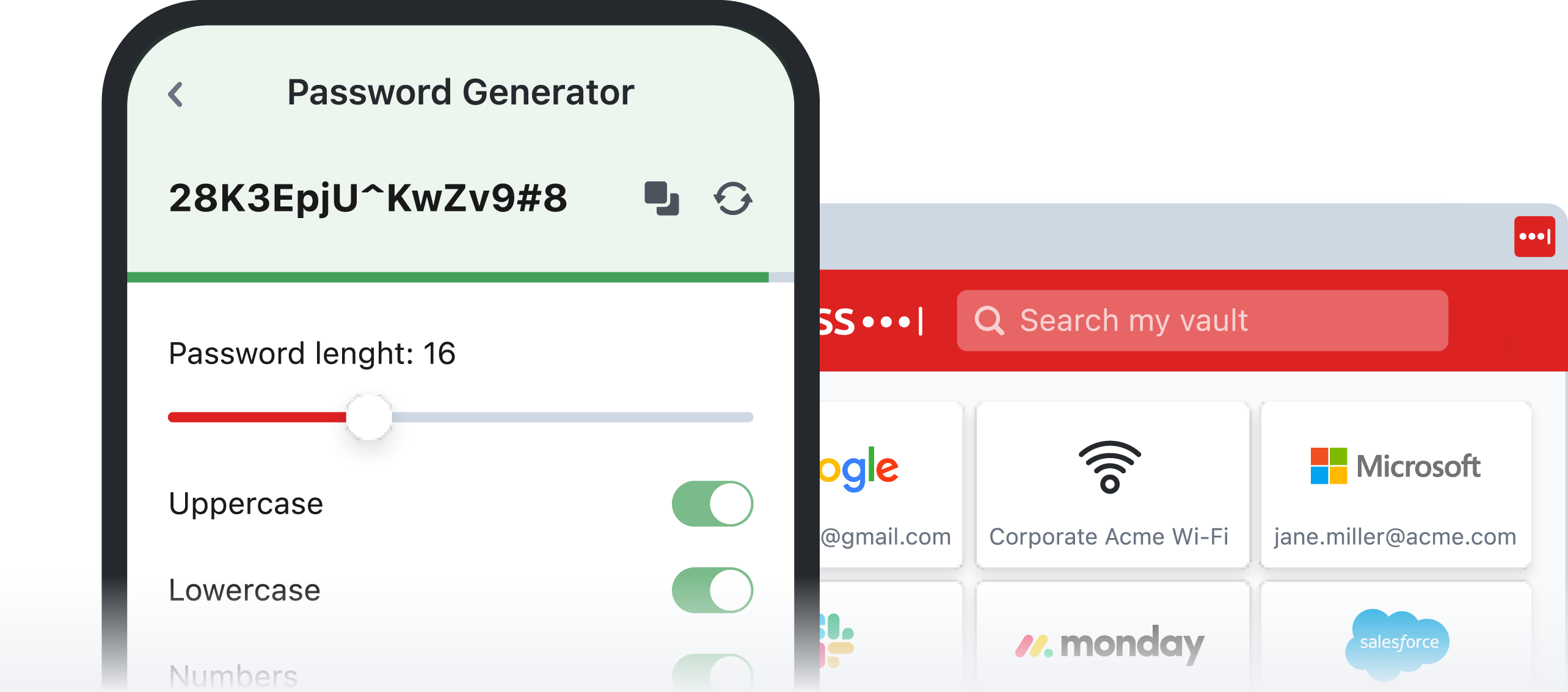
Did you know that the average person uses the same three to seven passwords to log in to over 170 online accounts? In addition to being reused, these passwords are often weak and can be easily guessed