If you’re building, renovating, or improving your home, there’s a new scam you need to watch for—and it’s catching people at exactly the wrong time.
How the Scam Works
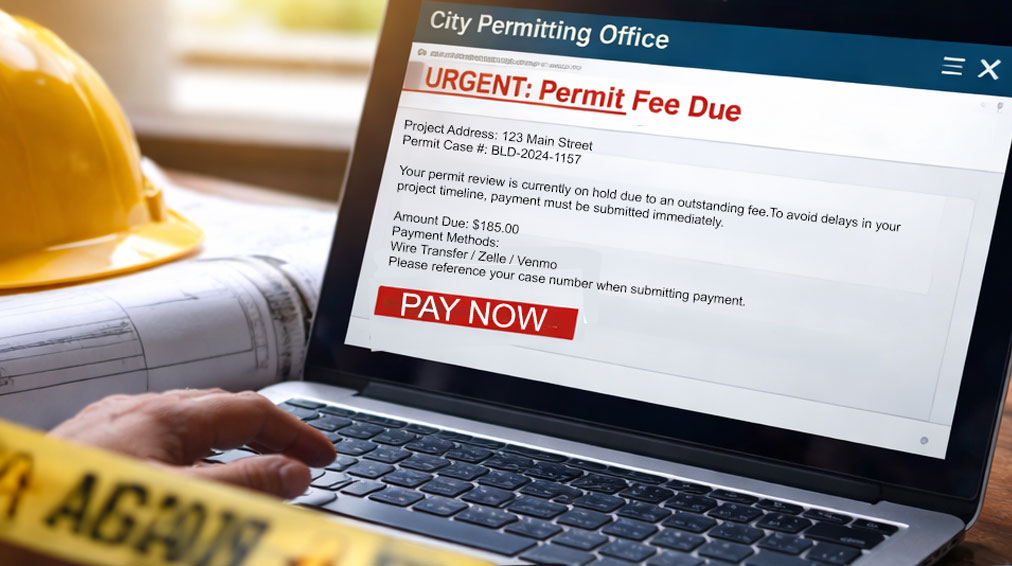
You receive an email that appears to come from a local government office—maybe your city, county, or permitting department.
The message claims there’s an issue with your project and that you must pay a permit fee immediately to avoid delays.
It looks legitimate.
It may include:
- Your home address
- A case or permit number
- The name of a real local official
The email then urges you to act quickly and pay using:
- Wire transfer
- Payment apps like Venmo or Zelle
- Cryptocurrency
Here’s the Truth
There is no fee.
There is no issue with your permit.
This is a scam.
Cybercriminals are using publicly available information—like property records and local government details—to make these messages look incredibly real. And because you may already be working on a project, the timing makes it even more convincing.
If you send payment, it goes directly to the scammer—and it’s almost impossible to recover.
Why This Scam Works
This attack isn’t about hacking systems—it’s about manipulating people.
Scammers rely on:
- Timing – catching you in the middle of a real project
- Urgency – pressuring you to act quickly
- Legitimacy – using real names, addresses, and agencies
It’s a reminder that today’s cyber threats often start with a simple message—not a technical breach.
How to Protect Yourself
Before you take action on any unexpected request, slow down and verify.
Keep these tips in mind:
- Don’t trust appearances – An email can look official and still be completely fake.
- Be skeptical of urgent payment requests – Government agencies do not demand immediate payment through wire transfers, payment apps, or cryptocurrency.
- Verify using official sources – If you receive an unexpected notice, contact your local office using the phone number on their official website—not the contact info in the email.
- When in doubt, pause – A few extra minutes of verification can save you thousands of dollars.
Stay Aware. Stay Protected.
Scams like this are becoming more targeted and more believable. Whether it’s a home project or your business, the best defense is awareness.
At Citynet, we’re committed to helping you stay informed about the latest threats—and providing the technology and support to keep you protected.