In recent years, high-profile ransomware attacks have shaken industries and organizations worldwide. As technology advances, so do the tactics employed by threat actors. However, a crucial and often underestimated element in these attacks is the human factor.
In the ever-evolving landscape of cyber threats, it is crucial to stay vigilant and informed to protect ourselves from falling victim to scams. This week, we shed light on a deceptive tactic that cybercriminals are employing –
Tax season is upon us and many anticipate their tax returns. However, with the annual arrival of tax season, there's also an unfortunate rise in malicious activities by cybercriminals seeking to take advantage of innocent taxpayers. Protect
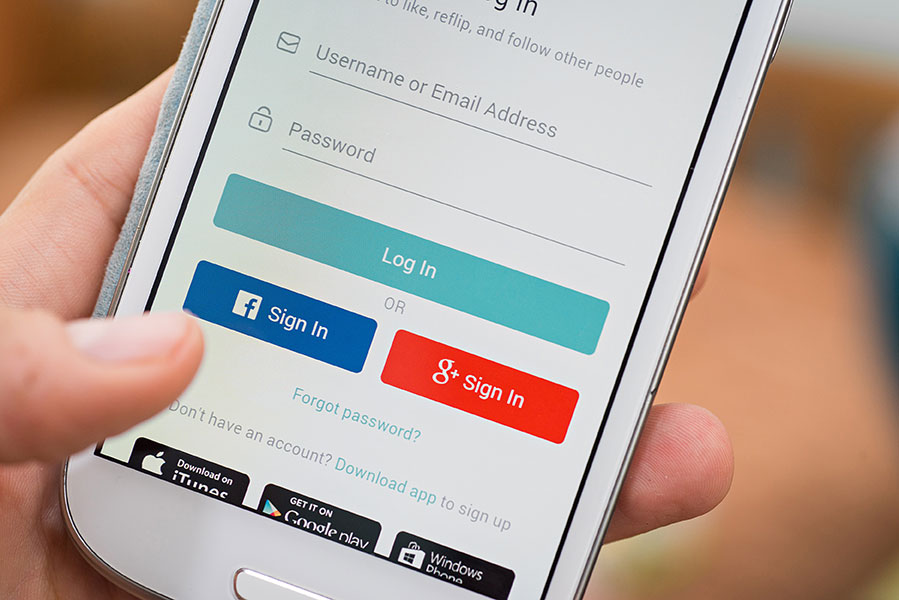
In today's digital age, the convenience of logging in with your Facebook or Google account seems like a time-saving solution. Many online platforms offer this option to streamline the account creation process, but is it really the
You likely use popular search engines like Google or Bing to explore topics of interest. Have you ever wondered how certain results end up at the top of the list? Unfortunately, cybercriminals can exploit search results to
Protect Yourself with These Tips In the ever-evolving landscape of online scams, cybercriminals continue to find new and convincing ways to trick users into divulging sensitive information. One such method gaining popularity is the "I Can't Believe
Elevating IT Support with Citynet's Managed Services In an era dominated by technological advancements, businesses rely heavily on seamless IT operations to thrive. However, the complex world of technology can often feel impersonal, leaving organizations longing for a
A colossal data breach comprising over 26 billion records has been uncovered by security researchers. This extensive collection of records originates from various sources, including LinkedIn, Twitter, Adobe, and numerous other organizations, making it potentially the largest
Cybersecurity Tips In a world where cybercriminals are constantly on the prowl, safeguarding your personal and work mobile devices has never been more critical. Citynet is committed to empowering people with the knowledge and tools needed to
Vendor Email Compromise (VEC), also known as "financial supply chain compromise," is a sophisticated form of Business Email Compromise (BEC) attack that specifically targets third-party vendors to exploit their relationships with customers. Attackers impersonate vendors to deceive