
Zero Trust Architecture: A Must-Have Strategy for Modern IT Security
In the ever-evolving landscape of cybersecurity, one trend stands out for its effectiveness in countering the sophisticated threats of today: Zero Trust Architecture (ZTA). As

In the ever-evolving landscape of cybersecurity, one trend stands out for its effectiveness in countering the sophisticated threats of today: Zero Trust Architecture (ZTA). As

In today’s digital age, protecting our online privacy has become increasingly important. Many users turn to incognito mode, also known as private browsing, believing it

90% involve social engineering (see infographic below) In the realm of cybersecurity, the ability to predict and prepare for attacks is invaluable. Much like how

How It WorksDeepfake technology uses artificial intelligence to mimic voices with astonishing accuracy. Scammers obtain samples of the target’s voice, often from social media or
Increased connectivity, coupled with the rise of remote and hybrid work, is prompting organizations to evolve their user access security and make strides toward a

In our digital age, where data is the new currency, network security is paramount. Yet, all too often, organizations find themselves engaged in a game

If you’re sticking to once-a-year sessions for your employees, it’s time to rethink your approach. Let’s face it, it’s likely dull and uninspiring. And if
In the vast landscape of the internet, myths and misconceptions often abound, shaping our perceptions and influencing our online behaviors. At Citynet, we’re committed to

Majority of Cyber Incidents Now Target Small & Medium Businesses (SMBs) Cybercrime is a pervasive threat that affects individuals across all socioeconomic backgrounds, yet its
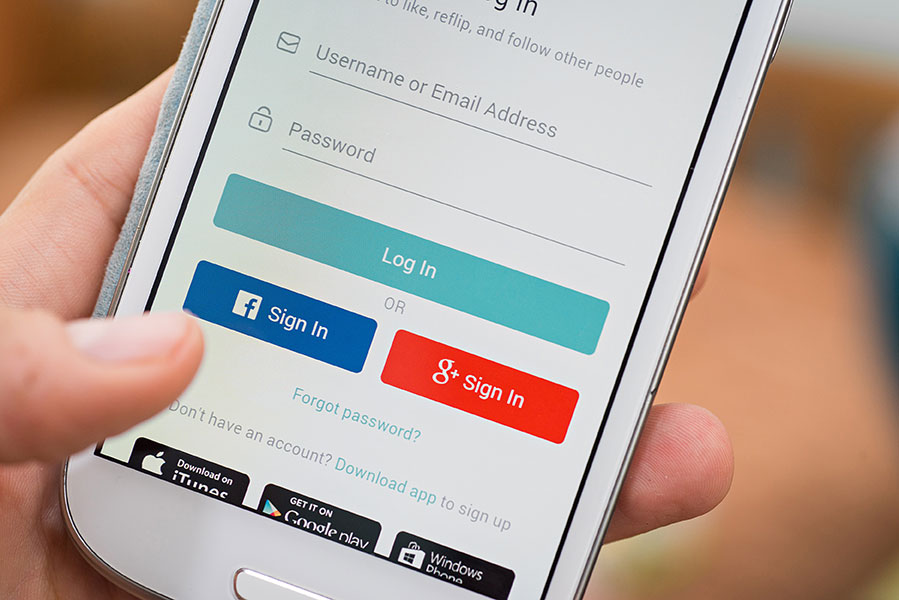
In today’s digital age, the convenience of logging in with your Facebook or Google account seems like a time-saving solution. Many online platforms offer this