The results of KnowBe4’s 2023 Phishing By Industry Benchmarking Report are in!
Highlights from the comprehensive report:
- In North America, ransomware continues to threaten organizations of all sizes and industries.
- Given the success of ransomware over the last few years, cybercriminals have not needed to make major changes to their tactics, which continue to create a lucrative and profitable business model for them. The ransomware-as-a-service (RaaS) model comprises many successful attacks in North America.
- Because most organizations have become reasonably good at restoring their data, in 2019, ransomware groups began to focus on getting access to and transferring data to use it as additional leverage. Cybercriminals know that information is power, and they use the threat of the public release of information as a significant source of leverage to get paid. This damages an organization’s reputation and can also be crippling from the potential fines from regulatory agencies.
- Less publicly visible but just as devastating, another type of cybercrime, business email compromise (BEC), continues to surface as a prolific attack type.
- One key differentiator of BEC compared to other types of cybercrime is that BEC typically does not include any attachment or link in the email, indicators that many people have become suspicious of and that technical controls have a chance at spotting. Instead, BEC relies purely on social engineering and emotional manipulation to drive victims to take the attacker’s intended action. BEC attacks are very effective because they prey on employees’ trust in their colleagues. In many cases, the victim will not even think to question the email’s authenticity and will simply follow the instructions.
- Vendor email compromise (VEC) is a growing threat to businesses. In a VEC attack, the attacker gains access to the email account of a trusted vendor and then uses that account to send fraudulent emails to the vendor’s customers.
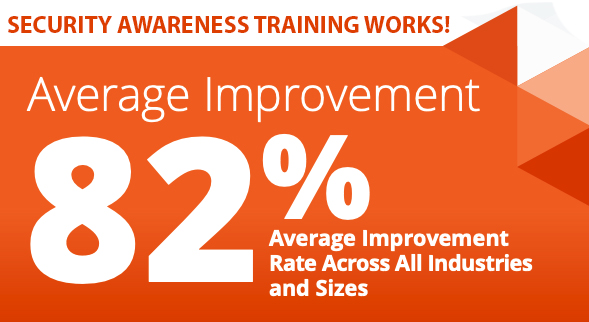
Train your employees to spot these tactics and keep your network safe! Citynet partners with security awareness training leader, KnowBe4 and offers a free trial of this vital security platform. Contact us today!